The DriftAlarm Methodology
Six phases of attacker-perspective assessment — from asset discovery to remediation roadmap. Every scan follows the same methodology used by professional penetration testers, automated and enhanced with AI.
SIX PHASES OF THE ASSESSMENT
Asset Discovery
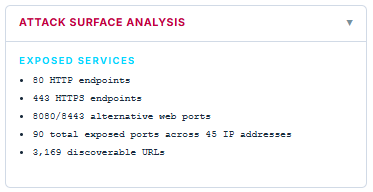
Map Your Entire External PerimeterBefore you can defend your organization, you need complete visibility. Our discovery engine maps every subdomain, IP address, open port, and running service — just like an attacker would during initial reconnaissance.
- ▹Subdomain enumeration (discovered 82 subdomains, 60 live)
- ▹IP address resolution across 45 addresses
- ▹Port scanning — 90 exposed ports identified
- ▹Technology fingerprinting — 33 technologies detected
- ▹Cloud infrastructure mapping
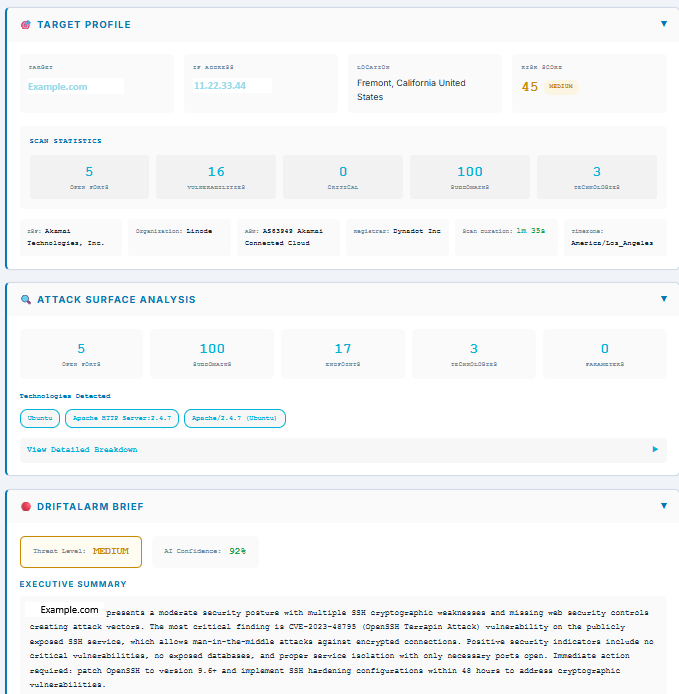
Vulnerability Assessment
Find Weaknesses Before Adversaries DoMulti-engine vulnerability detection correlates findings across industry-standard scanners and 10,000+ Nuclei templates to identify CVEs, misconfigurations, default credentials, and exposed services.
- ▹CVE detection with severity scoring
- ▹CISA Known Exploited Vulnerabilities (KEV) correlation
- ▹Configuration weakness identification
- ▹Default credential detection
- ▹Service-specific vulnerability checks
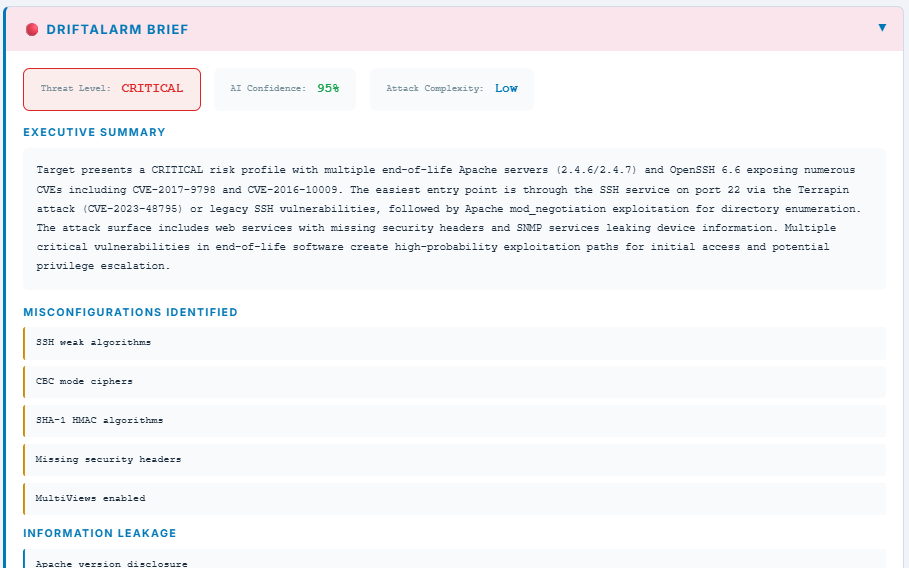
AI Threat Analysis
Intelligence, Not Just DataRaw vulnerability lists aren't actionable. Our AI analysis engine generates executive-ready security briefs that contextualize findings through real-world attack patterns, assign threat levels, and rate attack complexity.
- ▹AI-generated executive summary with confidence score
- ▹Threat level assessment (Critical / High / Medium / Low)
- ▹Attack complexity rating
- ▹Misconfiguration categorization
- ▹Information leakage identification
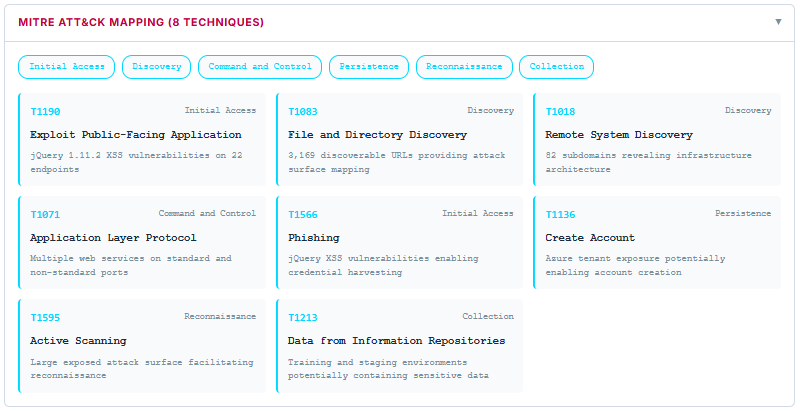
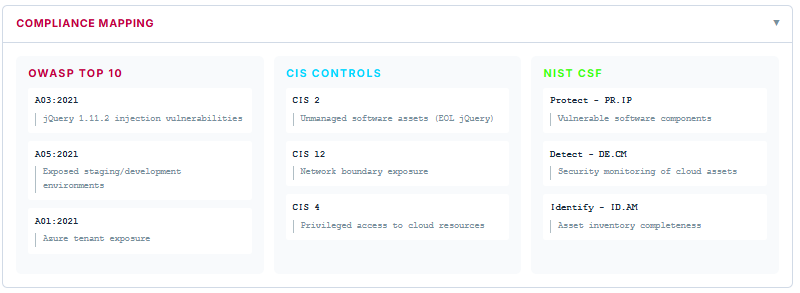
Framework Mapping
Align to Industry StandardsEvery finding is mapped to the frameworks your auditors, board, and compliance team care about. Communicate risk in a language stakeholders understand.
- ▹MITRE ATT&CK technique mapping (8+ techniques per scan)
- ▹OWASP Top 10 alignment
- ▹CIS Controls mapping
- ▹NIST Cybersecurity Framework correlation
- ▹Kill chain stage identification
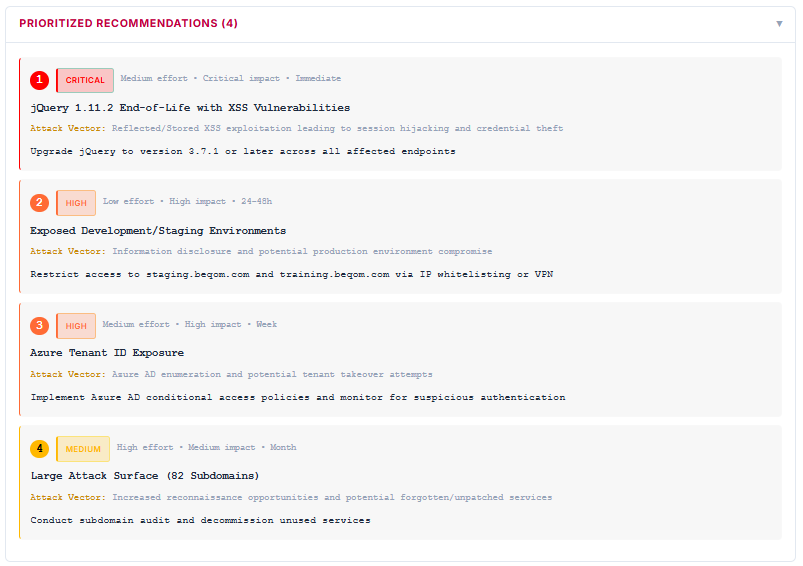
Remediation Roadmap
Fix the Right Things in the Right OrderEvery scan produces a prioritized remediation plan ranked by severity, effort, business impact, and timeline. Recommendations include specific attack vectors and technology-specific fix instructions — not generic advice.
- ▹Priority-ranked remediation (Critical → Low)
- ▹Effort and timeline estimates (Immediate / 24-48h / Week / Month)
- ▹Attack vector descriptions per finding
- ▹Technology-specific fix instructions
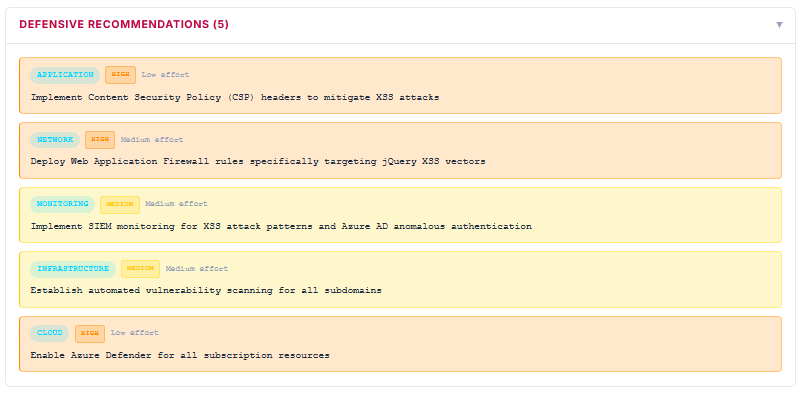
- ▹Defensive recommendations by category (Application, Network, Infrastructure, Cloud, Monitoring)
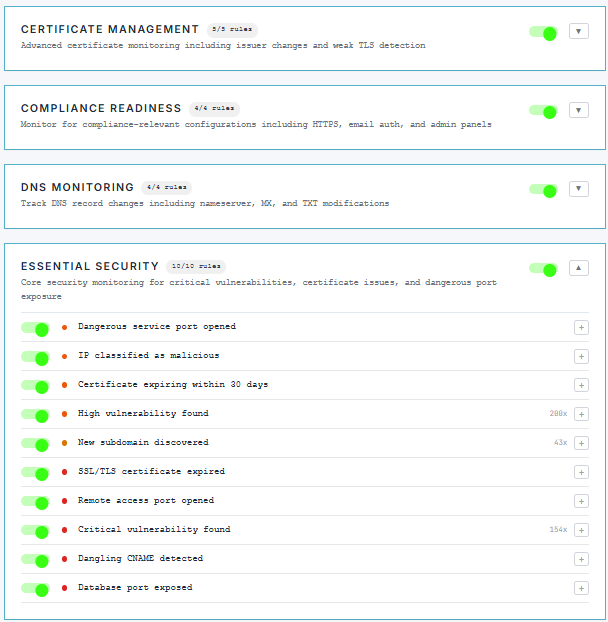
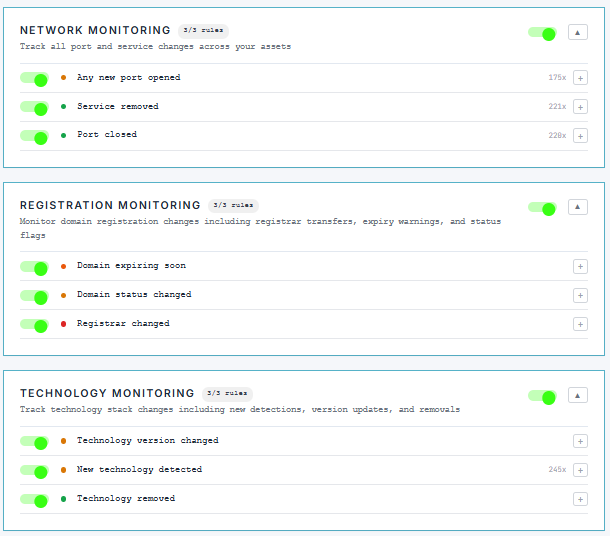
Continuous Drift Detection
Watch for Changes That Create RiskSecurity isn't a point-in-time assessment — it's continuous awareness. DriftAlarm monitors 41 conditions across 8 categories, alerting you the moment your attack surface changes. New ports, expired certificates, DNS modifications, technology changes — nothing drifts unnoticed.
- ▹41 detection rules across 8 categories
- ▹Certificate management monitoring (5 rules)
- ▹DNS and registration change tracking
- ▹Network port and service monitoring (with trigger counts — 175x-228x)
- ▹Technology stack drift detection (245x triggers)
- ▹Compliance readiness monitoring
Beyond Scanning: A Complete Security Toolkit

Vulnerability Validation
Don't just detect — validate. Test for XSS reflection, SQL injection, CORS misconfiguration, subdomain takeover, anonymous database access, and more. Prove vulnerabilities are real before escalating.
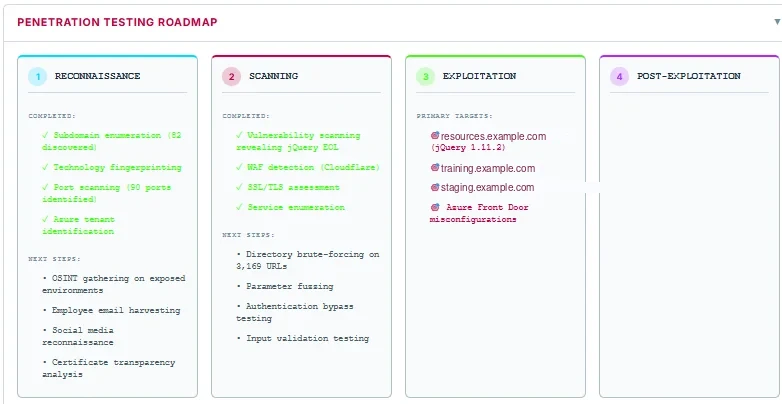
Penetration Testing Roadmap
Each assessment generates a structured pentest roadmap — from completed reconnaissance through exploitation targets. Know exactly where a professional pentester would focus next.
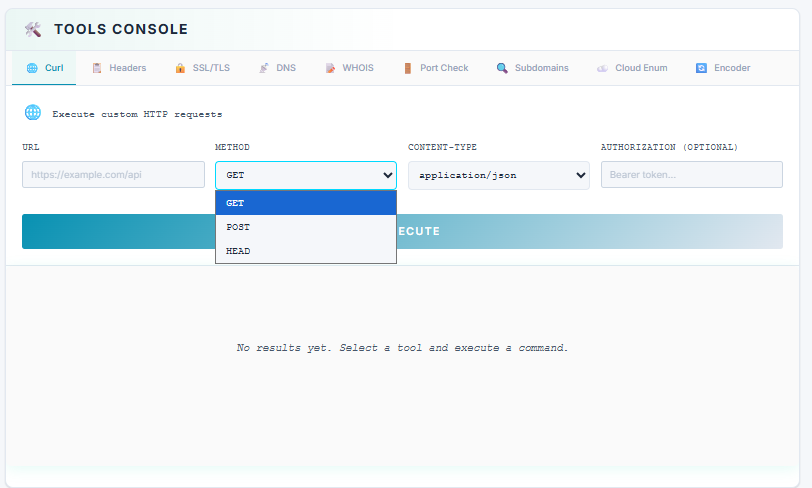
Built-In Security Tools
Curl, Headers analysis, SSL/TLS inspection, DNS lookup, WHOIS, Port Check, Subdomain enumeration, Cloud Enum, and Encoder — all from your browser. No terminal required.
Ready to See Your Attack Surface?
Add your first domain. Get results in 90 seconds. Full Standard access for 30 days.
No credit card • No sales call • Cancel anytime